Microsoft Azure -> Microsoft Azure
1. Introduction
The purpose of this Deployment guide is to demonstrate the way in which Dbvisit Standby 8.0 software can be used within the Azure Cloud Hosting Space. In this guide, we focus on both the Primary and Standby databases being hosted on MS Azure Windows 2016 Virtual Machines. In another document, we focus on 'On-Premise Primary' to Standby in the Azure Cloud. A link that document can be found here
2. Initial Setup and Configuration
2.1 Provisioning the Servers
Connect to Azure Portal and Select 'Compute' from the options for 'New'
In this guide, we are going to install and configure Dbvisit Standby on Windows so both Virtual Machines will be Windows Server 2016 Datacenter.
Clicking "create" directed us to a wizard with the following Steps.
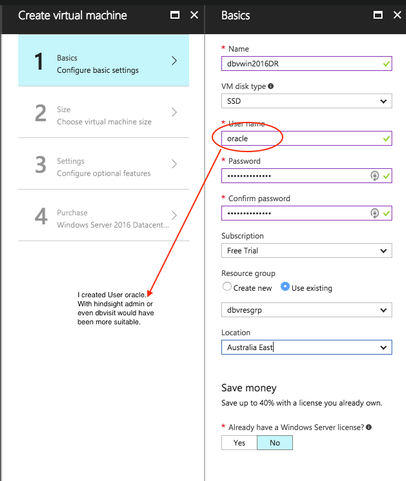
Step 1 "Basics": configures the name of the VM and adds an 'Admin User', Subscription and Resource Group. License details are also entered here. Choosing No for the Windows Server License here means the daily cost of the VM increases as the Windows Server License costs are bundled into the daily price for the VM.
There was already resource group 'dbvresgrp' created during a previous VM creation.
In the User Name box, 'Oracle' was entered. However, further on into the installation it was realised that choosing a more generic name such as dbvisit (admin is a reserved word and not allowed) would have made more sense. Creating a Windows VM meant that the Oracle binaries needed also to be installed (unlike when you chose an Oracle pre-built VM in Azure where the platform is Linux and the binaries are pre-installed). The installation of the Oracle binaries insisted that the installing user not be an administrator and suggested to create a new user. Therefore it was not possible to use the oracle user to install the binaries and instead user dbvisit was created. This, in turn, meant the $ORACLE_HOME didn't have 'oracle' in the directory_path. (A minor annoyance, but still worth a mention to think about the users before creating the VMs)
It was decided to keep this in the guide as an information point.
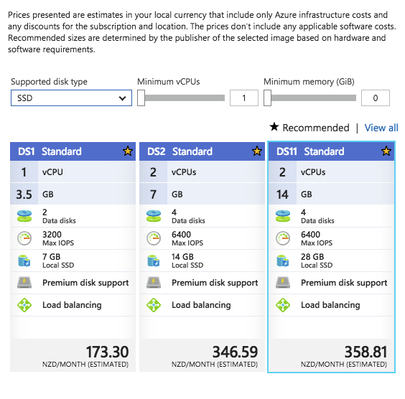
Step 2 "Choose Virtual Machine Size". The size of both VMs in this Guide is DS11 Standard consisting of 2 vCPUs, 14GB Memory and 28GB local SSD.
Throughout this guide, no mention is made about the licensing implications of running Oracle software on Microsoft Azure. The setup we have here has been built for demonstration purposes and falls within the scope of the Microsoft Azure 'free-trial'. Further information regarding Oracle Licenses in the cloud can be found here. Also Licensing Oracle Software in the Cloud Computing Environment.
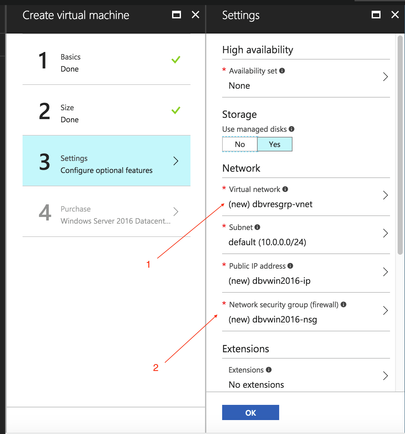
Specify the name of a new Virtual network (1) and Network Security Group (2).
The defaults were accepted for step 4 and the VM was created. This process was then repeated for the 2nd VM.
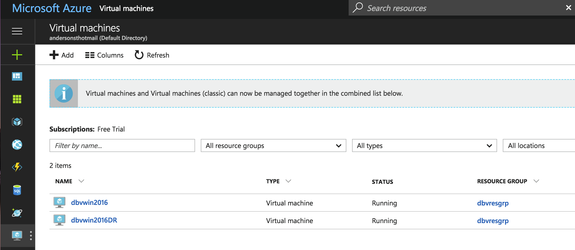
Then, 'click' on the VM icon on the taskbar to view the VMs.
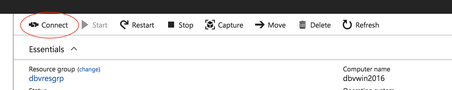
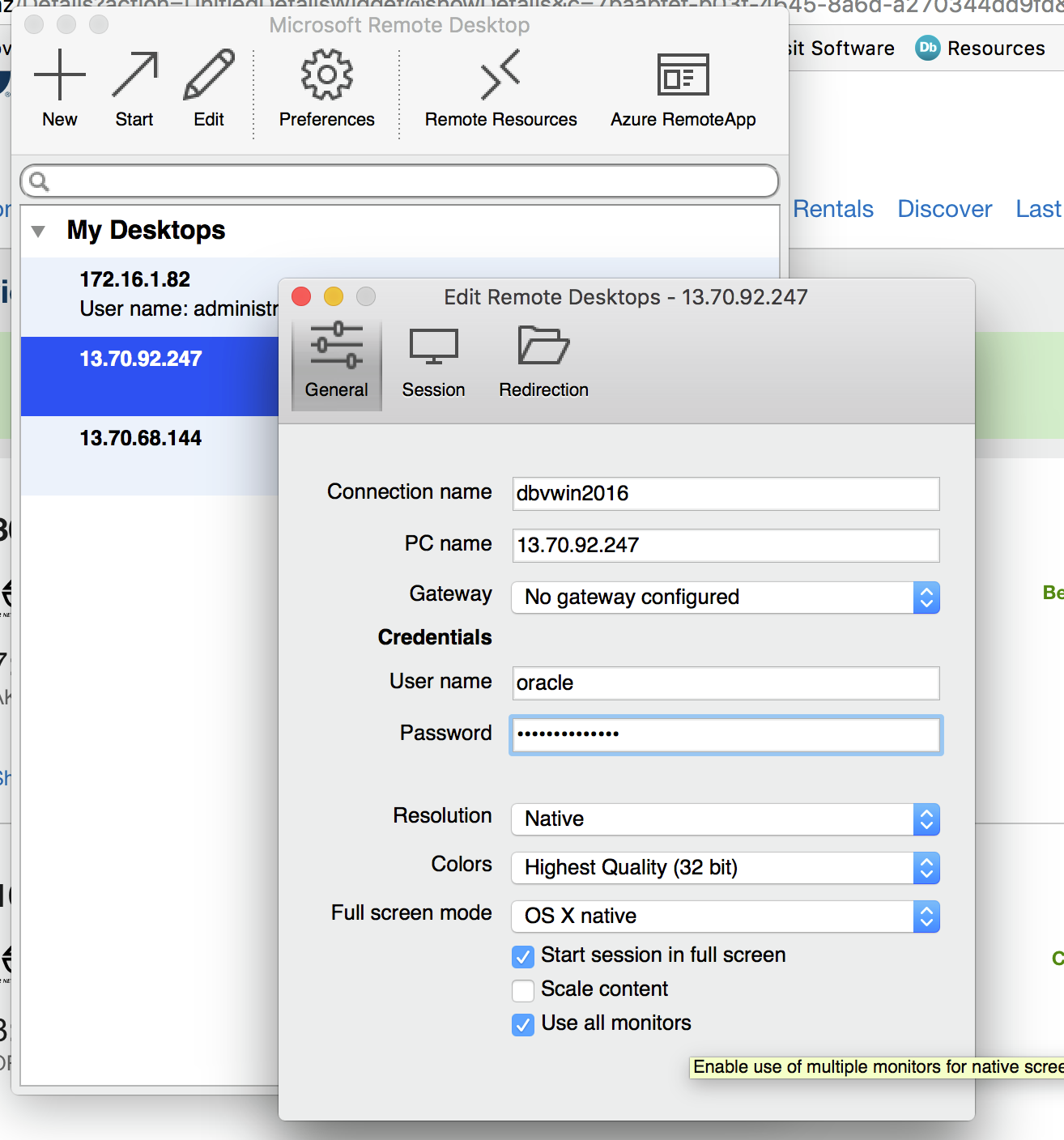
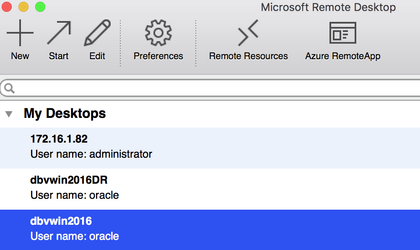
Connecting to each of the VM is via Microsoft Remote Desktop.
Within the dashboard home section of each VM, the connect icon downloads the RDP file required to connect.
The password details can be stored for each VM and the connection details adjusted to reflect the machine name instead of just the IP.
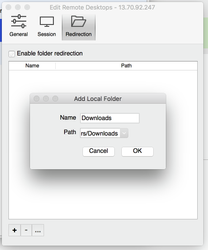
In addition to the clicking on the Redirection option allows a local drive to be mapped to the Machine. This was useful for copying both the Oracle and Dbvisit Standby binaries
Summary Details of the 2 VMs are as follows :
| Primary Server Details | Standby Server Details |
|---|---|
Name: dbvwin2016 vCPUs: 2 OS: Windows 2016 Datacenter Memory: 14G Storage: 28G Version: 12.1.0.2 Edition: Enterprise Edition Database: LAA Dbvisit Base: C:\Program Files\Dbvisit Standby Version: 8.0.14.19191 | Name: dbvwin2016DR vCPUs: 2 OS: Windows 2016 Datacenter Memory: 14G Storage: 28G Version: 12.1.0.2 Edition: Enterprise Edition Database: LAA Dbvisit Base: C:\Program Files\Dbvisit Standby Version: 8.0.14.19191 |
2.2 Preparing the Servers
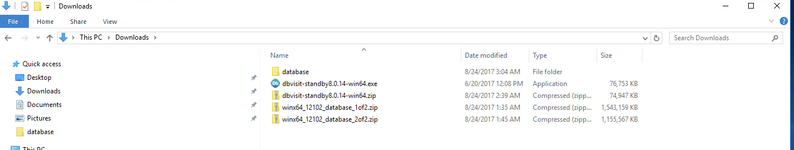
Connect to each of the servers using the Microsoft Remote Desktop details provided earlier and copy and then unzip the required binaries for the Oracle and Dbvisit Installations from the local mapped drive.
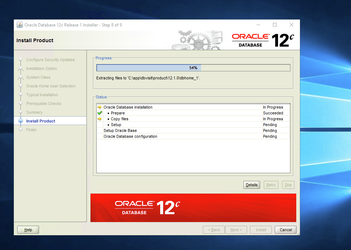
In-depth details regarding the Oracle Binaries installation are outwith the scope of this guide. However, Oracle 12c binaries were installed and a database running ARCHIVELOG mode pre-created under the new dbvisit user.
One other point to note. It was found to be easier to pre-create the user for the Oracle install rather than choose this option as part of the binary installation. The reason for this, when the user is created as a windows administrator, the password policy is adhered to. However, when a password is chosen as part of the binary installation unless you are confident the password adheres to the correct security policy no check is made until the create user step is reached. If the password doesn't fit the security standards, the installation fails and exits.
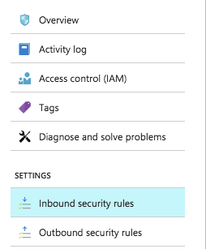
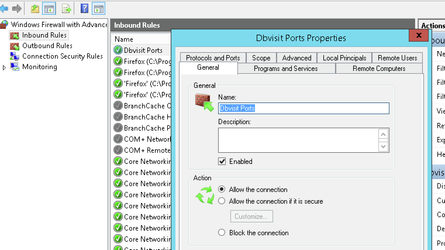
For Dbvisit Standby to communicate between the 2 hosts, and to enable access to the GUI frontend, 3 ports need to be made available. These are 7890 (Dbvnet), 7891 (Dbvagent) and 4433 (dbvserver: GUI). To do this, security rules need to be added to each Network Security Group for each node and, also inbound and outbound firewall rules need to be added to the VMs themselves.
E.g. For the Network Security Group Associated with the DR machine
Configure additional Inbound and Outbound Security rules. For ease, a range encompassing all 3 ports can be used (as is shown here). But for maximum security create one rule per port.
Inbound Rules
Outbound rules.
Perform the same task on each server.
In addition to this, add inbound and outbound firewall 'port' rules to the servers themselves.
When using 'New Rule Wizard', note that the default 'Action' for the outbound rule is 'Block the connection'. This needs to be set to 'Allow the connection' which is the default action for a new 'Inbound Rule'
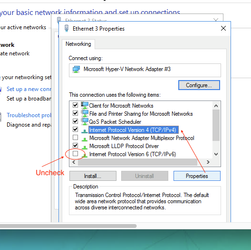
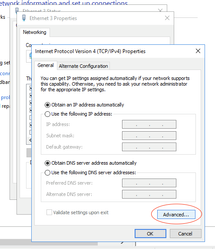
Windows 2016 Datacenter runs IPv6 by default. This must be disabled as the final step to allowing connections between the servers.
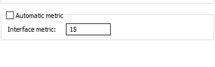
Begin by 'un-checking' the IPv6 and then select the 'properties' of IPv4, then 'Advanced' and Enter an 'Interface metric'
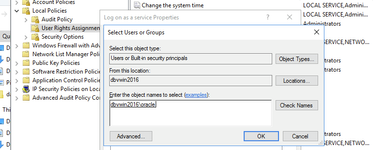
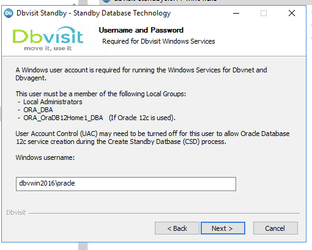
Once the firewall rules for inbound and outbound connections have been configured, ensure that the oracle user has the 'Log on as a service' Permission and is a member of the groups 'Local Administrators','ORA_DBA' and 'ORA_OraDB12Home1_DBA' (if 12c is used)
For further information regarding the pre-requisites for installing Dbvisit Standby v8 can be found here.
At this stage, the servers are ready for the next stage of installing the Dbvisit Standby software.
3. Install, Configure and Run the Standby software
3.1 Installing and Configuring the Software
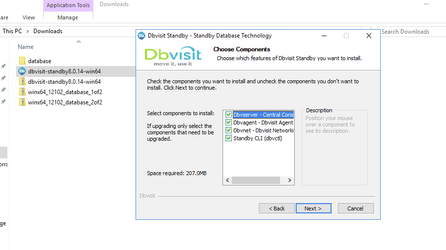
Unzip installer following the instructions in the dbvisit installation guide as an admin user (in this guide: user oracle).
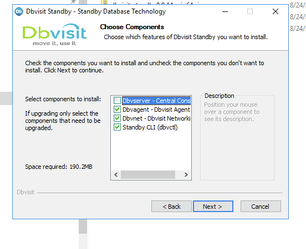
On the primary server (dbvwin2016) install the core components, leaving the box for the central console (Dbvserver) unchecked.
Once the correct username and password have been entered and verified the binaries will be installed.
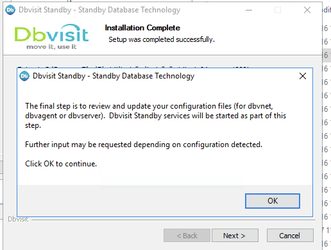
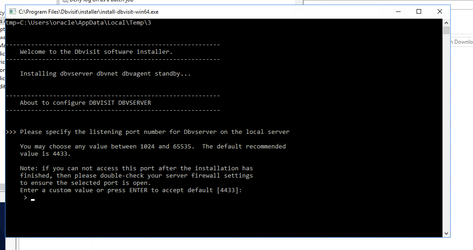
At the end of the installation, the component configuration will automatically be launched.
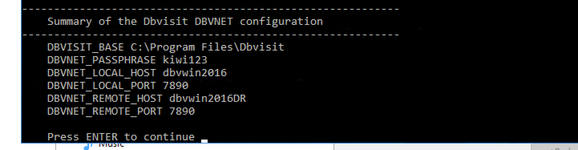
e.g. Dbvnet on the Primary Server
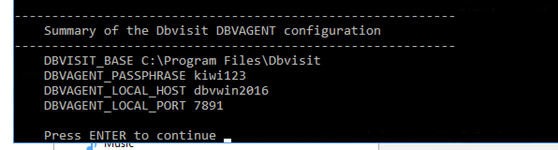
Dbvagent on the Primary Server
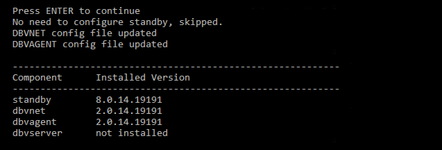
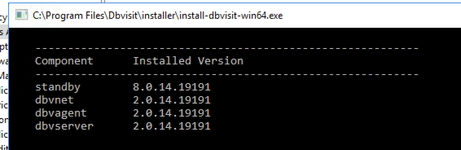
Installation Summary
Repeat the steps on the Standby Server this time also opting to install the Central Console
Dbvnet Configuration on the Standby Server.
The dbvagent installation on the standby server is not shown as the defaults were accepted.
Dbvserver configuration on the Standby Server
Installation Summary on the Standby Server
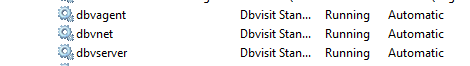
As part of the installation of Dbvisit Standby on Windows. The services for each component are created and automatically started (e.g. from DR Server)
Version 8.0.20 has a new parameter, that of DBVSERVER_PUBLIC_HOST (parameter public_address in dbvserver.conf)
Rather than accepting the default hostname prompt here, the public-facing IPv4 address of the Cloud Host should be used. Public-facing IPv4 address that will be supplied to the Agents (Dbvagent) to be used for pushing information back to the Central Console. This is the externally resolvable address supplied to dbvagent, not an additional listener address on dbvserver itself.
3.2 Start the GUI and Create the DDC
The following browsers are supported when using the Dbvisit Standby Web Based interface (latest versions recommended)
- Firefox
- Chrome
Future support for the following browsers are planned:
- Safari
- IE
Download and install either Chrome or Firefox.
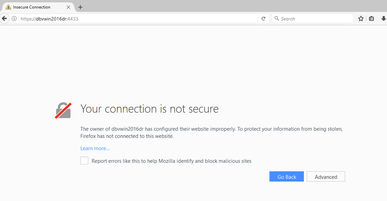
From within the browser navigate to the https://<dbvserver_host>:4433. In this case, the standby node
Click 'Advanced' and add the security exception to proceed to the login screen
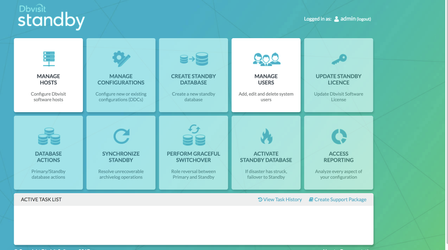
Enter the default username/password of admin/admin and proceed to the first screen, manage hosts.
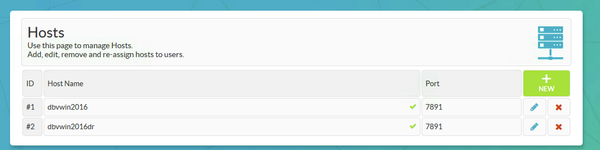
Each of the VMs was created using the same Virtual Network, therefore each host is already resolvable from the other using their machine name.
Enter each of the hosts in turn, specifying the passphrase used at creation time.
If either of the Host Names displays an x here, then check the firewall rules, the IPv6 settings, and the network security group rules for each server.
A useful test is to use telnet on the Dbvisit agent port to check connectivity
C:\Users\dbvisit>telnet dbvwin2016DR 7891
If a blank screen is returned then the port is open and available
Return to the Main Menu and then proceed on to creating the DDC
The creation of the DDC file is shown in the following steps.
Firstly Create a directory for ARCHSOURCE and ARCHDEST parameters.
The former is only required in the event of a Graceful switchover when the Primary becomes a Standby database. In this example, the same location is created on each server.
C:\app\oracle\dbvisit_arch
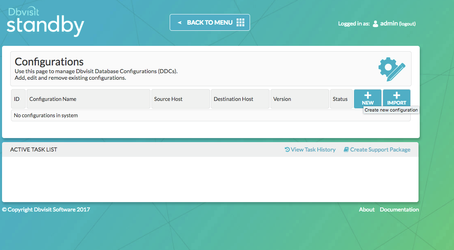
To create a DDC from the GUI. Choose the Manage Configurations Tab
Create a New Configuration. Fill out the relevant entries then click 'Submit'
We've opted not to show the DDC file creation from this installation due to the binaries being installed under a user that wasn't Oracle and don't want to add misdirection to the worked example. Instead, refer to the userguide section on creating the DDC.
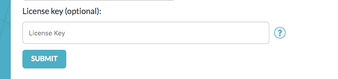
In Standby version 8.0.14 it is possible to enter the license details during the DDC creation, this option was chosen during the creation of this DDC file.
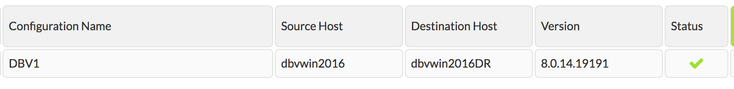
The configuration can be viewed and edited from the 'Manage Configurations' Tab.
3.3 Create the Standby Database
3.3.1 Creating the Standby with the GUI
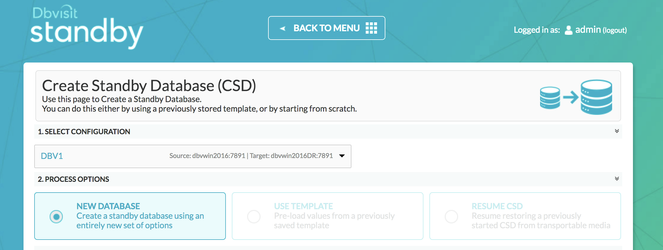
Choose the Create Standby Database Tab from the Home Screen.
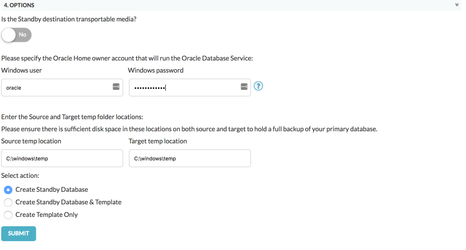
Select your configuration, New Database, edit the SPFILE parameters if required and then check there is enough space in the Source and Dest temp locations.
Click Submit. The progress can be monitored from the resulting icon in the status bar.
3.3.2 Creating the Standby with the CLI
To Create the Standby database with the command line is shown below
C:\Program Files\Dbvisit\Standby>dbvctl -d DBV1 --csd
>>> Running pre-checks please wait... done
What would you like to do:
1 - Create standby database (and optionally save settings in template)
2 - Help
3 - Terminate processing
Please enter your choice [1]: 1
-------------------------------------------------------------------------------
Answer Yes to transfer the datafiles directly to the standby server (not
recommended for large database or slow networks)
Note tablespaces will be placed in backup mode for direct copy.
Answer No (recommended) to create an RMAN backup of primary datafiles in a
temporary location and transfer the backup to the standby server
=>Do you want to copy database files directly to the standby server? [N]:
Your input: N
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
=>Do you want to use TRANSPORTABLE MEDIA to transfer the database backup to the
standby server? Transportable media is an external device such as a USB drive
that is first plugged into the primary server and then manually transferred to
the standby site and plugged into the standby server to continue the process.
It can be used for large databases or slow networks.
Specifying No means the network will be used to transfer the database backup.
[N]:
Your input: N
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
A temporary location must be specified on DBVWIN2016 where the database will be
backed up to first.
This location must be big enough to hold RMAN backup of the whole database
(1.29GB).
=>Specify the location on this server: [C:\windows\temp]:
Your input: C:\windows\temp
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
A temporary location must be specified on DBVWIN2016DR where the database
backup will be copied to before moving to specified locations.
=>Specify location on remote server: [C:\windows\temp]:
Your input: C:\windows\temp
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
Oracle Home User login might be required to create the Oracle Windows service
Leave empty if Oracle Home User is Windows built-in account
=>Specify Oracle Home User: []: oracle
Your input: oracle
Is this correct? <Yes/No> [Yes]:
=>Specify Oracle Home User password: []: *********
Your input: *********
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
=>Do you want to use an existing standby spfile rather than create a new one
from scratch? [N]:
Your input: N
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
=>Do you want to register a newly created standby database with Oracle Restart?
[N]: N
Your input: N
Is this correct? <Yes/No> [Yes]:
The following oracle database parameters will be set in the standby database pfile or spfile:
-------------------------------------------------------------------------------
SID NAME VALUE
* audit_file_dest C:\app\oracle\admin\LAA\adump
* compatible 12.1.0.2.0
* control_files C:\APP\ORACLE\ORADATA\LAA\CONTROL01.CTL,C:\APP\ORACLE\FLASH_RECOVERY_AREA\LAA\CONTROL02.CTL
* db_block_size 8192
* db_domain
* db_name LAA
* db_recovery_file_dest C:\app\oracle\flash_recovery_area
* db_recovery_file_dest_size 4102029312
* db_unique_name LAA
* diagnostic_dest C:\app\oracle
* dispatchers (PROTOCOL=TCP) (SERVICE=LAAXDB)
* log_archive_format ARC%S_%R%T.arc
* memory_target 2113929216
* open_cursors 300
* processes 150
* remote_login_passwordfile EXCLUSIVE
* spfile OS default
* undo_tablespace UNDOTBS1
-------------------------------------------------------------------------------
What would you like to do:
1 - Proceed with creating the standby database
2 - Edit oracle database parameters for the standby database pfile/spfile
3 - Terminate processing
Please enter your choice [1]:
Validating oracle database parameters... please wait
=>SUCCEEDED
-------------------------------------------------------------------------------
=>Create standby database template for DBV1 using provided answers? [Y]:
Your input: 1
Is this correct? <Yes/No> [Yes]:
-------------------------------------------------------------------------------
=>Continue with creating a standby database? (If No processing will terminate,
the saved template will be available for future use) [Y]:
Your input: 1
Is this correct? <Yes/No> [Yes]:
>>> dbvctl will now run a pre-flight check for standby database creation. An attempt will
be made to create a standby (s)pfile using oracle standby database parameters, followed
by trying to start the standby instance. If this step fails, then please double-check
the following items before re-running dbvctl again:
1) Review the standby database parameters you have supplied and provide valid values
unless a template is used.
2) Recreate the template to provide valid values for standby database parameters if a
template is used.
>>> Running pre-flight check for standby creation, please wait... done
>>> Total database size for LAA is 3.35GB
>>> Backing up primary database...
Backing up datafile 1... done
Backing up datafile 3... done
Backing up datafile 4... done
Backing up datafile 5... done
Backing up datafile 6... done
Backing up datafile 7... done
Backing up datafile 8... done
Backing up datafile 9... done
>>> Creating standby control file... done
>>> Transferring backup from DBVWIN2016 to DBVWIN2016DR...
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_1_3ESDNA8M_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_1_3FSDNA9F_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_2_3GSDNA9I_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_3_3HSDNAA2_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_4_3ISDNAA4_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_5_3JSDNAAG_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_6_3KSDNAA3_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_7_3LSDNAA1_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_8_3MSSAAA3_1_1.RMAN... done
Transferring C:\windows\temp\DBV_DBV1_CSD_DBF_9_3NSOKUA1_1_1.RMAN... done
>>> Restoring standby control files... done
>>> Starting standby database LAA on DBVWIN2016DR mount... done
>>> Restoring datafiles on DBVWIN2016DR...
Restoring datafile 1... done
Restoring datafile 2... done
Restoring datafile 3... done
Restoring datafile 4... done
Restoring datafile 5... done
Restoring datafile 6... done
Restoring datafile 7... done
Restoring datafile 8... done
Restoring datafile 9... done
>>> Renaming standby redo logs and tempfiles on DBVWIN2016DR... done
>>> Performing checkpoint and archiving logs... done
>>> Completing standby database creation... done
>>> Standby database created.
To complete creating standby database please run dbvctl on the primary server first,
then on the standby server, to ensure the standby database is in sync with the primary
database.
PID:3816
TRACE:3816_dbvctl_csd_DBV1_201709051722.trc
3.4 Performing Basic Tasks
Some examples of basic tasks are outlined below. Please refer to the online documentation for more details on each command.
3.4.1 Log Gap Report
Run a log gap report from the Primary Site
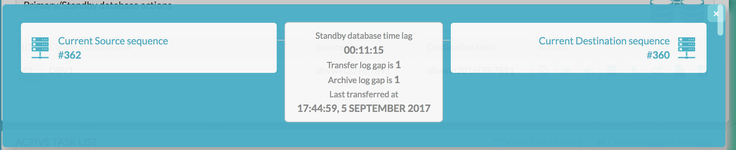
C:\Program Files\Dbvisit\Standby>dbvctl -d DBV1 -i ============================================================= Dbvisit Standby Database Technology (8.0.14.19191) (pid 3808) dbvctl started on DBVWIN2016: Tue Sep 5 17:53:15 2017 ============================================================= Dbvisit Standby log gap report for DBV1 thread 1 at 201709051753: ------------------------------------------------------------- Destination database on DBVWIN2016DR is at sequence: 360. Source database on DBVWIN2016 is at log sequence: 362. Source database on DBVWIN2016 is at archived log sequence: 361. Dbvisit Standby last transfer log sequence: 360. Dbvisit Standby last transfer at: 2017-09-05 17:44:59. Archive log gap for LAA: 1. Transfer log gap for LAA: 1. Standby database time lag (DAYS-HH:MI:SS): +00:08:14. ============================================================= dbvctl ended on DBVWIN2016: Tue Sep 5 17:53:17 2017 ============================================================= C:\Program Files\Dbvisit\Standby>
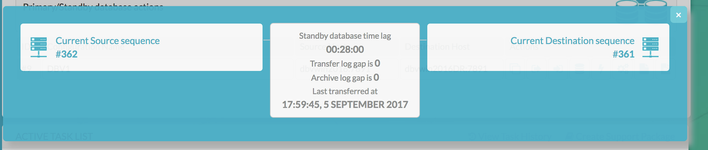
Also from the GUI
3.4.2 Log Transfer
Sending the logs from the Primary via the CLI
C:\Program Files\Dbvisit\Standby>dbvctl -d DBV1 ============================================================= Dbvisit Standby Database Technology (8.0.14.19191) (pid 3952) dbvctl started on DBVWIN2016: Tue Sep 5 17:59:38 2017 ============================================================= >>> Obtaining information from standby database (RUN_INSPECT=Y)... done Note FORCE_LOGGING is disabled in the primary database. >>> Sending heartbeat message... skipped >>> Transferring Log file(s) from LAA on DBVWIN2016 to DBVWIN2016DR for thread 1: thread 1 sequence 361 (O1_MF_1_361_DTWGGRRN_.ARC) ============================================================= dbvctl ended on DBVWIN2016: Tue Sep 5 17:59:46 2017 =============================================================
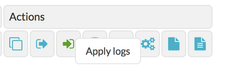
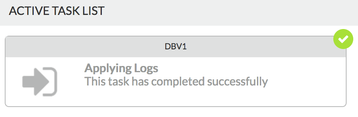
Apply Logs at the Standby Site via the GUI
3.4.3 Daemon Status
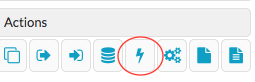
Start the Daemons for automatic send/apply from the GUI Database Actions Tab.
The lightning bolt icon manages the daemon processes.
When started on both sites they Log gap managed automatically and if no natural log switches have occurred, the daemon will also signal a log switch to keep the standby LAG to the desired amount. More information regarding the daemon settings can be found here in Section 4
https://dbvisit.atlassian.net/wiki/display/DS8QSG/Dbvisit+Standby+Scheduling
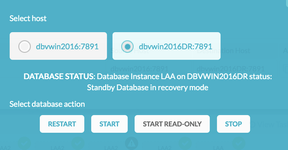
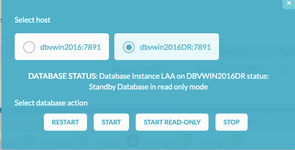
3.4.4 Starting Standby Database in Readonly Mode
From the Database Actions Tab choose the Database Icon. This allows the user to perform database actions on each node.
Before the Standby Database can be opened in readonly mode, there must be a log gap of 0 between the 2 systems.
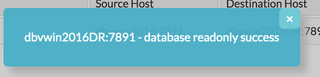
Select the Standby Host, review the current status and Select Start READ ONLY.
Now, the status is Read Only for the standby database.
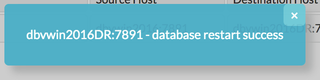
To switch back again. Choose Restart
Now the Standby is back in recovery mode and the logs can be applied as normal.
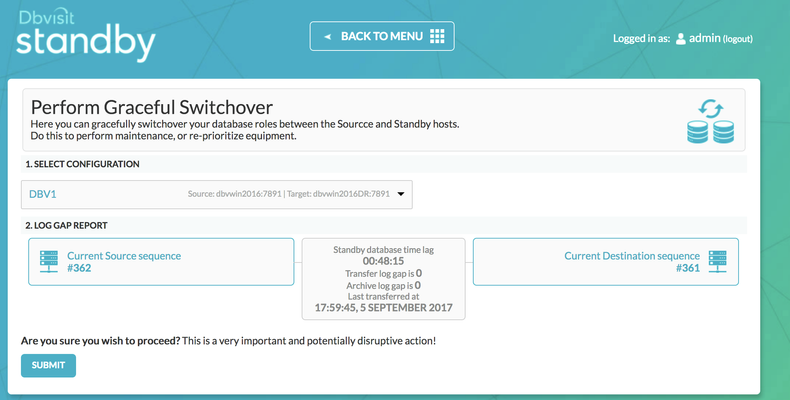
3.5 Performing Graceful Switchover
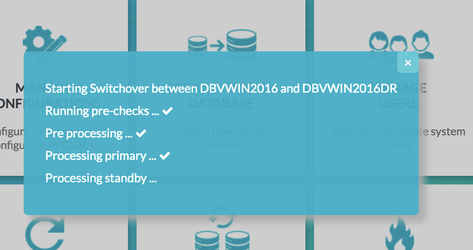
The following screenshots show a Graceful Switchover from one Cloud Standby to the other using the GUI. A first pre-requisite is to ensure that the daemons started earlier are not running whilst the switchover is in progress.
3.5.1 Check the Status of the Daemons
If the daemons have been started in the previous step, they need to be stopped before performing a graceful switchover.
3.5.2 Graceful Switchover Icon GUI
3.5.3 Check Log Gap is Zero and Click Submit
3.5.4 Locate the Task on the Task Bar
3.5.5 Monitor the Activity
3.5.6 Verify the New Roles within each of the Databases
Verify the new database roles within the database
C:\Program Files\Dbvisit\Standby>hostname dbvwin2016 C:\Program Files\Dbvisit\Standby> sqlplus / as sysdba SQL*Plus: Release 12.1.0.2.0 Production on Thu Jun 1 00:38:14 2017 Copyright (c) 1982, 2014, Oracle. All rights reserved. Connected to: Oracle Database 12c Standard Edition Release 12.1.0.2.0 - 64bit Production SQL> select name, database_role from v$database; NAME DATABASE_ROLE --------- ---------------- LAA PHYSICAL STANDBY C:\Program Files\Dbvisit\Standby>hostname dbvwin2016DR C:\Program Files\Dbvisit\Standby> sqlplus / as sysdba SQL*Plus: Release 12.1.0.2.0 Production on Thu Jun 1 00:38:14 2017 Copyright (c) 1982, 2014, Oracle. All rights reserved. Connected to: Oracle Database 12c Standard Edition Release 12.1.0.2.0 - 64bit Production SQL> select name, database_role from v$database; NAME DATABASE_ROLE --------- ---------------- LAA PRIMARY
3.6 Activate the Standby Database
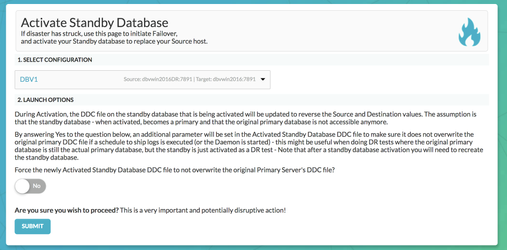
It is possible to activate the Standby Database and make it become the new Primary. This is also called failover to the standby database.
The assumption is that the original Primary site has been lost and needs to be rebuilt.
From the Central Console/GUI Choose the "Activate Standby Database Command"
3.6.1 Choose the Activate Standby Database
3.6.2 Select the Configuration
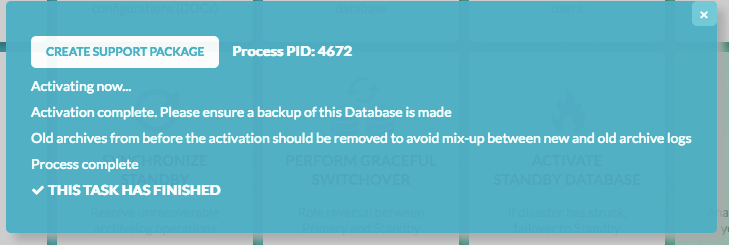
3.6.3 Monitor the Task from The Task Bar
3.6.4 Verify the Status within the Database
C:\Program Files\Dbvisit\Standby>hostname dbvwin2016 C:\Program Files\Dbvisit\Standby> sqlplus / as sysdba SQL*Plus: Release 12.1.0.2.0 Production on Thu Jun 1 00:38:14 2017 Copyright (c) 1982, 2014, Oracle. All rights reserved. Connected to: Oracle Database 12c Standard Edition Release 12.1.0.2.0 - 64bit Production SQL> select name, database_role from v$database; NAME DATABASE_ROLE --------- ---------------- LAA PRIMARY
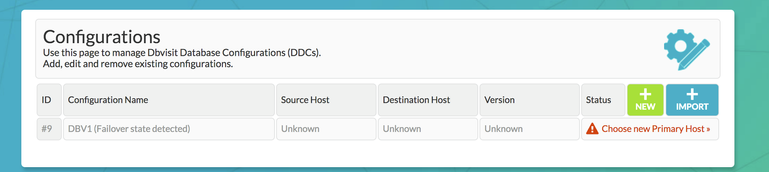
3.6.5 Manage Configurations Tab Implications
Now the Manage Configurations Tab has the option to choose the hosts. This allows you to either accept the current configuration with the new Primary (old Standby site) or start again with the original Primary site and depends on the circumstances of the Activation.